PDFtk actually isn't needed. It was being used for breaking a PDF into pages but this is something that be replaced by the already present 'pdftoppm'. Furthermore, by removing this dependency we contribute to reproducible builds and overall supply chain security because it was obtained from gitlab with no signature verification or version pinning. The replacement 'pdftoppm' enabled us to do a shortcut: - before: PDF -> PDF pages -> PNG images -> RGB images - after: PDF -> PPM images -> RGB images And this last conversion step is trivial since the RGB format we were using is just a PPM file without the metadata in its header. |
||
|---|---|---|
| .circleci | ||
| assets | ||
| container | ||
| dangerzone | ||
| dev_scripts | ||
| install | ||
| share | ||
| tests | ||
| .gitignore | ||
| BUILD.md | ||
| CHANGELOG.md | ||
| INSTALL.md | ||
| LICENSE | ||
| Makefile | ||
| poetry.lock | ||
| pyproject.toml | ||
| README.md | ||
| RELEASE.md | ||
| setup-windows.py | ||
| setup.py | ||
| stdeb.cfg | ||
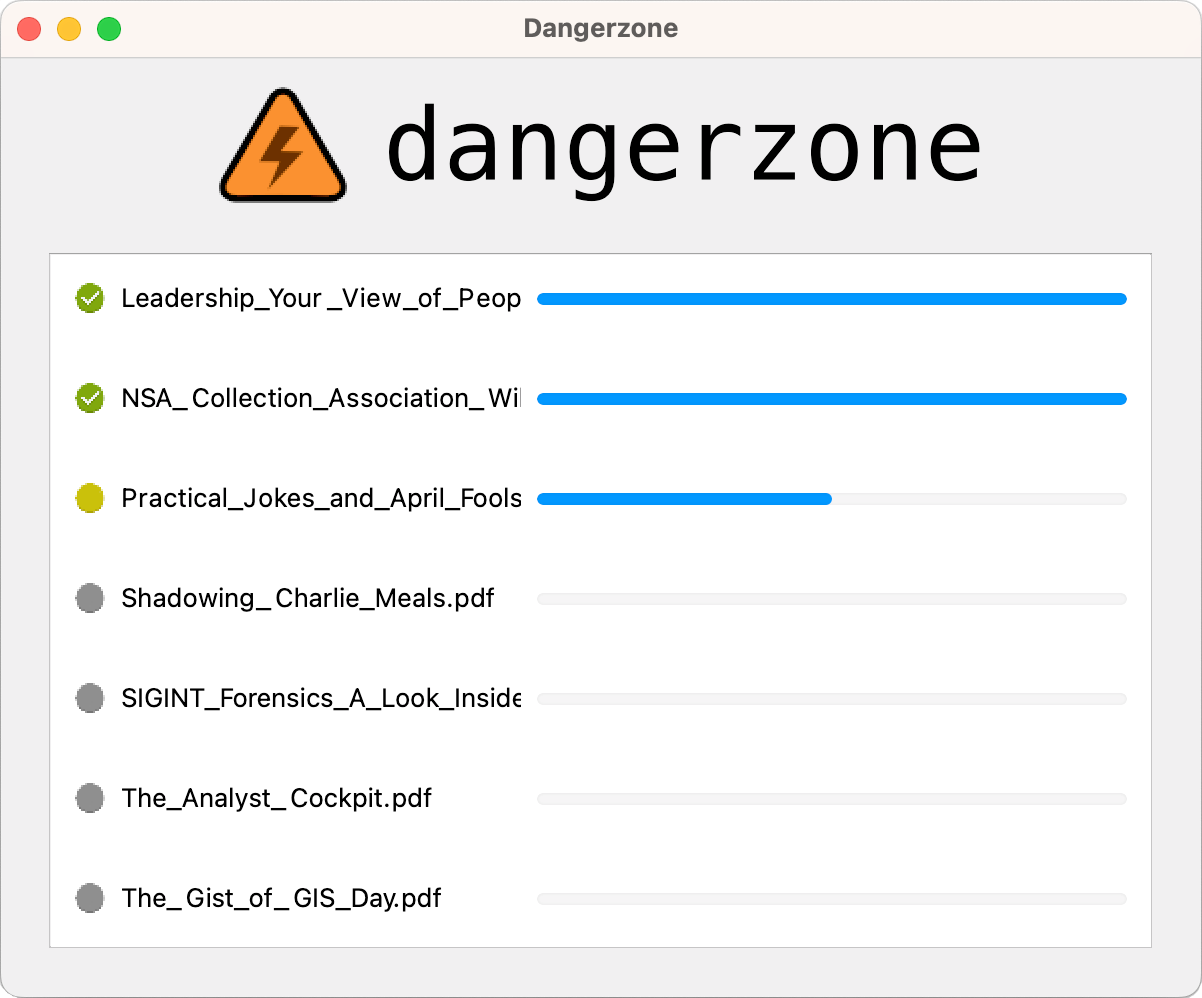
Dangerzone
Take potentially dangerous PDFs, office documents, or images and convert them to a safe PDF.
 |
 |
|---|
Dangerzone works like this: You give it a document that you don't know if you can trust (for example, an email attachment). Inside of a sandbox, Dangerzone converts the document to a PDF (if it isn't already one), and then converts the PDF into raw pixel data: a huge list of RGB color values for each page. Then, in a separate sandbox, Dangerzone takes this pixel data and converts it back into a PDF.
Read more about Dangerzone in the blog post Dangerzone: Working With Suspicious Documents Without Getting Hacked.
Getting started
- Download Dangerzone 0.4.0 for Mac
- Download Dangerzone 0.4.0 for Windows
- See installing Dangerzone for Linux repositories
You can also install Dangerzone for Mac using Homebrew: brew install --cask dangerzone
Some features
- Sandboxes don't have network access, so if a malicious document can compromise one, it can't phone home
- Dangerzone can optionally OCR the safe PDFs it creates, so it will have a text layer again
- Dangerzone compresses the safe PDF to reduce file size
- After converting, Dangerzone lets you open the safe PDF in the PDF viewer of your choice, which allows you to open PDFs and office docs in Dangerzone by default so you never accidentally open a dangerous document
Dangerzone can convert these types of document into safe PDFs:
- PDF (
.pdf) - Microsoft Word (
.docx,.doc) - Microsoft Excel (
.xlsx,.xls) - Microsoft PowerPoint (
.pptx,.ppt) - ODF Text (
.odt) - ODF Spreadsheet (
.ods) - ODF Presentation (
.odp) - ODF Graphics (
.odg) - Jpeg (
.jpg,.jpeg) - GIF (
.gif) - PNG (
.png)
Dangerzone was inspired by Qubes trusted PDF, but it works in non-Qubes operating systems. It uses containers as sandboxes instead of virtual machines (using Docker for macOS, Windows, and Debian/Ubuntu, and podman for Fedora).
Set up a development environment by following these instructions.